
Whether you share your Windows 7/8/10 with someone or not, keeping the folders locked and secure is crucial. If you lock the folders in Windows, it means that you are investing in the security of your documents. The more serious you are about the folders on your computer, the more protected the content inside the folder will be. Think about it once, you have shared your computer with someone without a password protecting a folder in Windows 7, and your folder has some confidential data, probably, office-related or your personal banking related. The person using your computer finds them and ends up damaging them, how would it feel?
Not that every person you share your computer with is untrustworthy, but they might click the delete button by mistake. And things like these are pretty common. This is why you should learn how to put a password on a folder in Windows 7. If you are serious about protecting your data, find out the best ways to lock your drive. Here, in this post, we will share a detailed guide about how to lock a folder in Windows 7; keep reading.
Table of Contents
Why Should You Lock and Password Protect Your Windows 7 Folder?
The most important reason why you should password protect a folder of Windows 10 or 7 using a password is to keep the data inside that folder safe and secure. As we said, mistakes can happen. If your child ends up using your computer when you are not around, they may click the delete button, not even this; what if you are sharing your computer with a colleague and they end up doing this? In-office situations, deletion of data often happens. Mostly non-intentional and when they are in a hurry.
Leave anyone else, imagine being in a hurry and end up deleting a file from a folder that you needed, and you remember clearing your recycle bin just a few seconds back. These are the situations why you should be ultra-careful. Folders that contain confidential and sensitive data must be password protected thinking about the future repercussions. Once you add a password and lock your folders, you can share your computer with whoever you want because you know your data is entirely safe.
Of course, adding a password will need some time investment, but nothing can be as damaging as losing essential data from the computer. So, what you can do is put a password separately on every folder; else, use a third-party tool to encrypt the complete folder. Don’t worry; we will help you learn how to do that conveniently.
Before you decide to add a password or encrypt a folder, learn the difference between the two. When you password-protect a folder, you are basically restricting someone from accessing it. They will be able to see the folder but won’t be able to access it since it will ask for a password. It works like the key of your door.
Now, encryption scrambles all the letters in a document so that your file becomes unreadable. Basically, after encrypting your file, what others will be seeing is ciphertext. Even in this case, they will need a key; once they have it, they will have the unscrambled text of the file.
Lock a Folder in Windows 7/8/10 Using BitLocker
If you don’t want to use any third-party tool, then you can try using the in-built function of Windows 7 to lock the folder of your computer. And the tool to use is BitLocker. This tool comes built-in in Windows 7 Ultimate and Enterprise editions. Once you password-protect your folder using the BitLocker tool, you will restrict other people from gaining access to your folders. So, the person trying to access the folder needs to have the correct password to do so.
What BitLocker does is that it encrypts the complete folder. It works on TPM, which is a trusted platform module. When a TPM chimp is enabled, it will provide the folder with advanced security features, making it impossible for random people to access the locked folder. In addition to this, TPM even protects against automated dictionary and guessing attacks. Here are the steps that you need to follow:
Step 1: Browse through the folder on your Windows 7 that you want to encrypt. Once you find it, right-click on it and then click on the Properties option.
Step 2: Now, click on the Advanced option. Advanced Attributes window will pop up. Here, you need to check the box for “encrypt contents to secure data.” After that, click on the OK option.
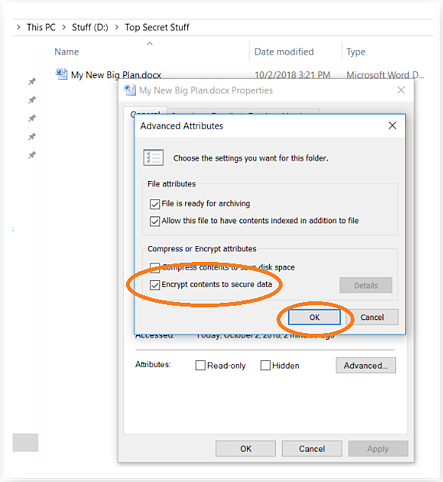
Step 3: The next option that you will see is how to encrypt your data. Whether you want to encrypt only the file, all the files, or the complete folder, the recommended thing is to lock the whole folder.
The folder, file, or files will be locked after you follow the steps, and you will be able to see a small yellow icon right on top of the folder, file, or files. This tells you that the file is locked. If you have locked an entire folder, you can add more files to it to encrypt the recent files automatically.
Password Protect a Folder in Windows 7 Using Folder Locker
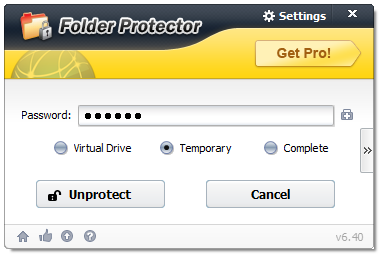
If you find the steps for using BitLocker a bit challenging, you can try a trusted third-party tool to lock your folder in Windows 7. And the recommended tool to use is KakaSoft Folder Protector. This professional Folder Protector will keep your folders safe and protected from unauthorized access. Once you encrypt the folder, all the essential files inside the folder will be restricted from unwanted usage and access. So, no matter how many files you have and what kind are inside that folder, you can lock it conveniently. Here are the steps that you need to follow:
Step 1: First things first, visit the official website of Kaksoft to download and install KakaSoft Folder Protector. Once done, you need to launch the program on your program.
Step 2: Once it is launched, you will see an icon of the folder; please click that to add the folder you protect and encrypt.
Step 3: You will be asked to enter a password to lock the folder. Enter the password twice as asked in the software. After that, you need to click on the Protect option to lock the folder, and that’s about it.
Bonus Tips for Folder and File Security
- There are a few things that you need to remember when you encrypt a folder with a password. Even if you lock your folder, never forget that there is nothing called a 100% protected folder. We are living in a high-tech world, and there are myriads of readily available instructions and tools available that can break into a folder that is password protected. But, do keep your folder protected because decoding the password for a folder will take time and a good amount of effort. If you have sensitive and confidential files in some of the folders, we recommend using a third-party tool because their encryption level is better and superior.
- Always make it a habit to create a backup for your files. The files are saved in a folder, and the folders are ultimately saved on your computer. In case of virus infestation, you can end up losing all the password-protected files and folders as well. Don’t forget that you have only password-protected your data to make them inaccessible by anyone else. But that doesn’t make them undeletable. They can be deleted when there is a virus or malware attack. They can be deleted by you as well. You may have entered the password to open the files, but you have clicked the delete option by mistake.
- Whenever you add a password to your files and folders, ensure to create a strong password that is hard to decode. However, at the same time, you need to remember the password that you have used. Try to create a password that will have upper case and lower case, both, along with some numeric and symbols. These kinds of passwords are always strong and challenging to crack. Back in 2012, hackers built a cluster that could easily guess passwords. And what it did was it guessed 350 billion passwords per second. And this was back in 2012; we are now living in a more advanced world, so imagine, how smart the hackers must have become. Therefore, save yourself from such circumstances and create a password that will be difficult to crack.
Conclusion
Always remember to password-protect your file because you never know what may happen to them. Ensure to create backups for both the password-protected and non-protected files so that even if you lose them somehow, you at least have the backup to work on. Use KakaSoft Folder Protector if you have essential documents and files to hide and protect. KakaSoft Folder Protector will let you protect all kinds of files in a folder. To download, visit the official website today.